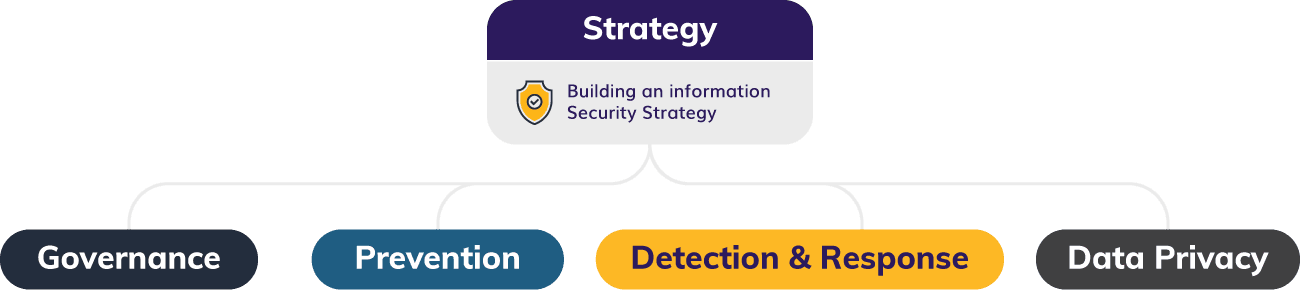
Security is a high-stakes game that affects the ability to provide quality products and services, both short-term and long-term. The costly financial and brand reputation impacts of data breaches are making cybersecurity consulting a board-level topic.
As a full-service business and technology consulting company, we’re the right partner to activate your cybersecurity program across an array of project types.
Centric’s Cybersecurity Consulting Services are designed to help address your most pressing security concerns by guiding you in:
- Establishing enterprise-level governance programs
- Implementing policies that directly address cybersecurity risks
- Driving business continuity through incident response and disaster recovery plans
- Addressing third-party vendor and service provider risks
- Regularly testing infrastructure and business applications